Documentation
Duo Trusted Endpoints - Ivanti Endpoint Manager Mobile (formerly known as MobileIron Core)
Last Updated: May 16th, 2024Contents
Certificate-based Trusted Endpoint verification for Ivanti Endpoint Manager Mobile will reach end-of-life in a future release. Migrate existing iOS Certificate Configuration management integrations to iOS Configuration. Learn more about the end-of-life timeline and migration options in the Duo Trusted Endpoints Certificate Migration Guide.
Duo's Trusted Endpoints feature secures your sensitive applications by ensuring that only known devices can access Duo protected services. When a user authenticates via the Duo Prompt, we'll check for the access device's management status. You can monitor access to your applications from trusted and untrusted devices, and optionally block access from devices not trusted by your organization.
Trusted Endpoints is part of the Duo Essentials, Duo Advantage, and Duo Premier plans.
Before enabling the Trusted Endpoints policy on your applications, you'll need to deploy the Duo device certificate or REST API access for Duo to your managed mobile devices. This guide walks you through Ivanti Endpoint Manager Mobile configuration for Android and iOS mobile devices.
These instructions are for the on-premises Ivanti Endpoint Manager Mobile software, version 11.8 and up. This integration may also work for MobileIron Core software 9.3 to 11.6, but navigation steps and input label may differ. If you are using Ivanti Neurons for MDM (formerly known as MobileIron Cloud and Ivanti Secure UEM), see our instructions for Ivanti Neurons for MDM instead.
Mobile Trusted Endpoints and Verified Duo Push: Trusted endpoint verification of iOS and Android devices with Duo Mobile uses the standard Duo Push approval process and will not prompt for a Duo Push verification code, even if the effective authentication methods policy for the user and application has "Verified Duo Push" enabled.
Prerequisites
- Access to the Duo Admin Panel as an administrator with the Owner, Administrator, or Application Manager administrative roles.
- Access to the Ivanti Endpoint Manager Mobile admin portal as an administrator with the rights to create roles, accounts, certificate authorities, device profiles, and register Android and iOS devices.
Android Configuration
Duo determines trusted device status on Android devices by leveraging the installed and activated Duo Mobile application on a given device to verify device information. To enable this verification you'll need to grant Duo read-only access to those devices via your Ivanti Endpoint Manager Mobile MDM's API access.
You must have already configured Android for Work in Ivanti Endpoint Manager Mobile.
Create the Ivanti Endpoint Manager Mobile Integration
- Log in to the Duo Admin Panel and navigate to Trusted Endpoints.
- If this is your first management integration, click the Get started button at the bottom of the Trusted Endpoints introduction page. If you're adding another management integration, click the Add Integration button you see at the top of the page instead.
- On the "Add Management Tools Integration" page, locate Ivanti Endpoint Manager Mobile in the list of "Device Management Tools" and click the Add this integration selector.
- Choose Android from the "Recommended" options, and then click the Add button.
The new Ivanti Endpoint Manager Mobile integration is created in the "Disabled" state. You'll turn it on when you're ready to apply your Duo trusted endpoints policy.
Please note that this integration takes advantage of managed app configuration and therefore Duo Mobile must be installed by your MDM for the device to be considered trusted.
Keep the Duo Admin Panel open in your browser. You'll need to refer back to the Ivanti Endpoint Manager Mobile management integration page to complete the Android configuration steps.
Configure Duo Mobile Distribution
-
Log on to the Ivanti Endpoint Manager Mobile admin portal as an administrator and navigate to Apps → App Catalog.
-
Click Add+ and then click Google Play.
-
In the "Application Name" field, enter in Duo Mobile, and then click Search. Select Duo Mobile and click Next.
-
Edit the Duo Mobile app description and categories if you wish. Click Next.
-
Enable the Install this app for Android for Work and By distributing this app you will accept the following permissions on behalf of users options for Duo Mobile.
-
Scroll down to "Configuration Choices". Locate the "Default Configuration" section and click on it to expand.
-
Enter $DEVICE_UUID$ into the "Trusted Endpoint Identifier" field.
-
Return to the Duo Admin Panel. Copy the Trusted Endpoints configuration key (it will look similar to DPK0W0KLPJLOGSKHTDD) and paste it into the Ivanti Endpoint Manager Mobile Trusted Endpoints Configuration Key field.
-
Click Finish to return to the App Catalog.
-
Select the Duo Mobile app. Click Actions → Apply to Labels. Select the labels that represent the user populations who will receive the Duo Mobile app.
-
Click Apply.
Create a Duo API Account
-
While still logged in to the Ivanti Endpoint Manager Mobile admin portal as an administrator, navigate to Devices & Users → Users.
-
Click the Add button and choose Add Local User on the pop-up menu.
-
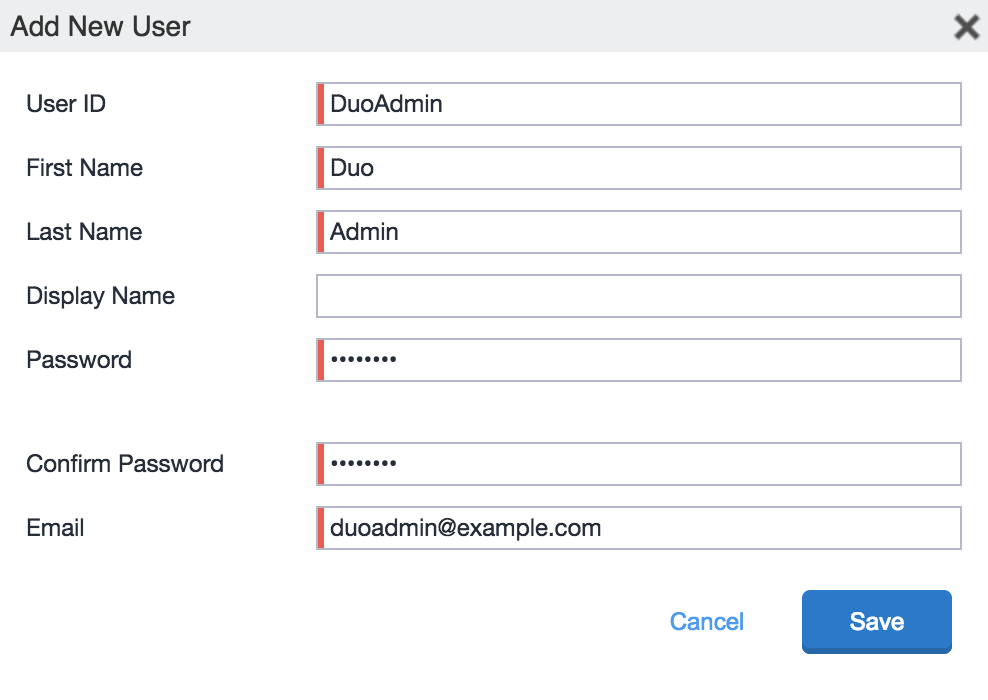
Enter the following information on the "Add New User" form:
User ID Enter the desired Duo account username. First Name and Last Name Enter a first and last name for the Duo API user (e.g. "Duo" "Admin"). Password and Confirm Password Enter and confirm a strong password for the Duo admin user. Email Address Enter an email address for the Duo admin user. -
Click the Save button to create the Duo admin user.
-
Navigate to Admin → Admins. Select the Duo Admin user you just created, click the Actions button, and then click Assign to Space.
-
Select a space from the "Select Space" drop-down list, and then check the box for the View device page, device details role under "Device Management". Click Save.
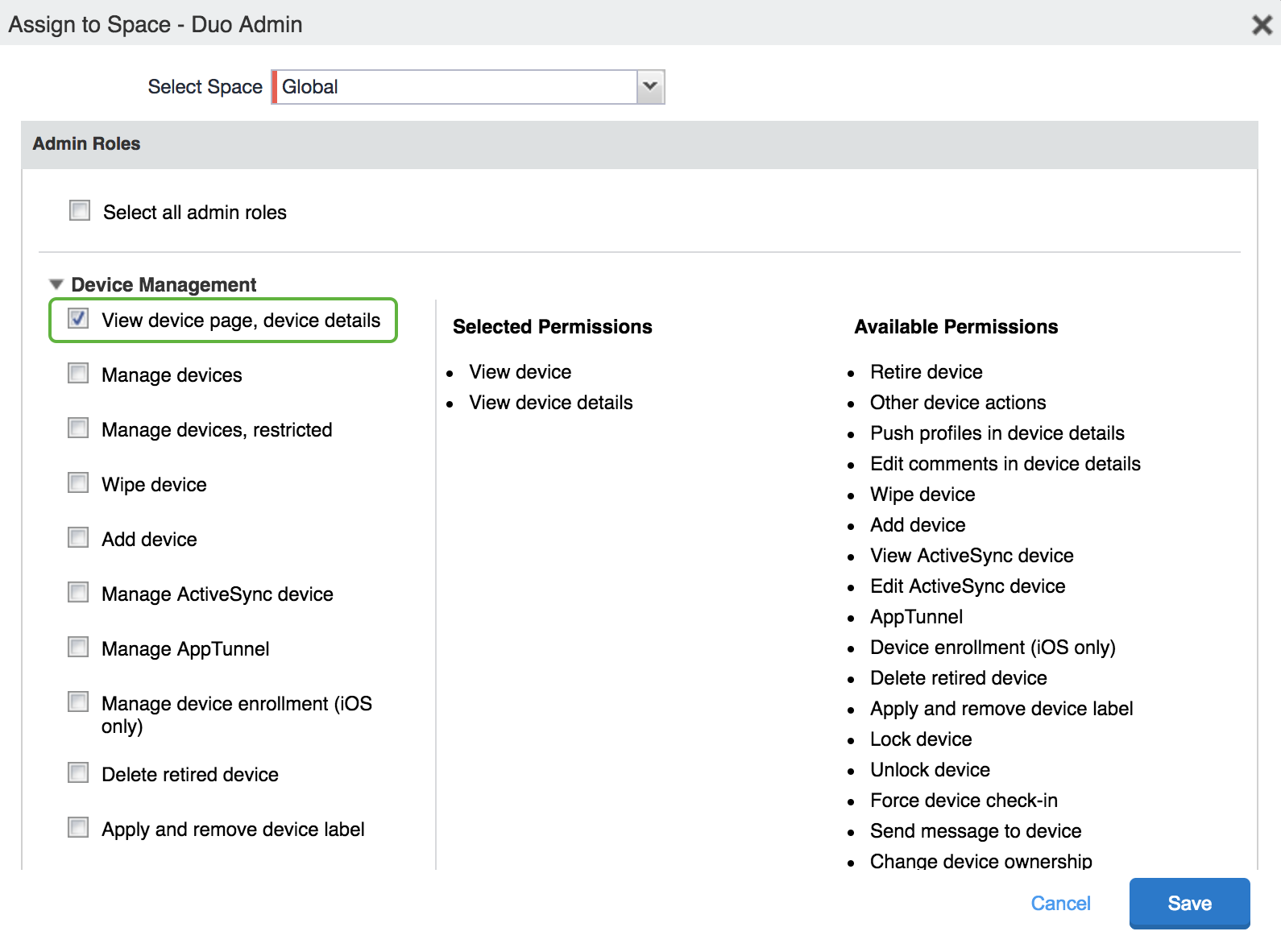
-
Repeat steps 5 and 6 for all available spaces that contain managed devices.
Enter Ivanti Endpoint Manager Mobile Info in Duo
-
Return to the Duo Admin Panel. Enter the following information into the blank fields in the "Enter API Details" section:
Local User Email Address Enter the email address (which is also the username) of the Duo admin user you created in Ivanti Endpoint Manager Mobile. Local User Email Password Enter the password for the Duo admin user you created in Ivanti Endpoint Manager Mobile. Ivanti Endpoint Manager Mobile Domain Name Enter your organization's Ivanti Endpoint Manager Mobile domain name. For example, acmecorp.mobileiron.com. -
Click the Test Configuration button to verify Duo's API access to your Ivanti Endpoint Manager Mobile instance. You'll receive a "Configuration Successful!" message if everything's correct. If the test fails, verify that you completed the Ivanti Endpoint Manager Mobile configuration steps and entered the right information in the Duo Admin Panel.
-
After you successfully test your configuration, click the Save & Configure button.
At this point, the configured integration is disabled and applies to no users until you finish your deployment.
Verify Android Device Information with Search
After you configure the connection between Ivanti Endpoint Manager Mobile and Duo you can verify that a given device's information is being pulled into Duo by searching for the device identifier from the Duo Admin Panel. See Search for Device Identifiers to learn how.
iOS Configuration
Duo determines trusted device status on iOS devices by leveraging the installed and activated Duo Mobile application on a given device to verify device information. To enable this verification you'll need to grant Duo read-only access to those devices via your Ivanti Endpoint Manager Mobile MDM's API access.
Before proceeding, configure the TLS trust certificate chain for mobile management for Ivanti Endpoint Manager Mobile.
Create the Ivanti Endpoint Manager Mobile with App Config Integration
- Log in to the Duo Admin Panel and navigate to Trusted Endpoints.
- If this is your first management integration, click the Get started button at the bottom of the Trusted Endpoints introduction page. If you're adding another management integration, click the Add Integration button you see at the top of the page instead.
- On the "Add Management Tools Integration" page, locate Ivanti Endpoint Manager Mobile in the list of "Device Management Tools" and click the Add this integration selector.
- Choose iOS from the "Recommended" options, and then click the Add button.
The new Ivanti Endpoint Manager Mobile with App Config integration is created in the "Disabled" state. You'll turn it on when you're ready to apply your Duo trusted endpoints policy.
Please note that this integration takes advantage of managed app configuration and therefore Duo Mobile must be installed by your MDM for the device to be considered trusted.
Keep the Duo Admin Panel open in your browser. You'll need to refer back to the Ivanti Endpoint Manager Mobile with App Config management integration page to complete the configuration steps.
Configure Duo Mobile Distribution
-
Log on to the Ivanti Endpoint Manager Mobile admin portal as an administrator and navigate to Apps → App Catalog.
-
Click Add+ and then click iTunes.
-
In the "Application Name" field, enter in Duo Mobile, and then click Search. Select Duo Mobile and click Next.
-
Edit the Duo Mobile app description and categories if you wish. Click Next.
-
Optionally pick a category, then click Next.
-
On the "App Configuration" screen, enable the following "Managed App Settings":
- Send installation request or send convert unmanaged to managed app request (iOS 9 and later) on device registration or sign-in
- Enforce conversion from unmanaged to managed app (iOS 9 or later)
-
Return to the Duo Admin Panel. Click the Download the App Config XML spec link. The downloaded app_config_spec.xml file will be needed to complete the "Managed App Configurations" section within Ivanti Endpoint Manager Mobile.
-
In Ivanti Endpoint Manager Mobile under the "Managed App Configurations" section, click Add+.
-
Click Choose File and select the app_config_spec.xml file you downloaded from the Duo Admin Panel. Do not drag and drop the .xml file into Ivanti Endpoint Manager Mobile as this may cause upload errors.
Once you upload the .xml spec file, the "MANAGED APP CONFIGURATIONS" information will show the Duo "trustedEndpointIdentifier" and "trustedEndpointConfigurationKey" keys and values.
-
Click Add and then click Finish.
-
Return to the App Catalog. Select the Duo Mobile app. Click Actions → Apply to Labels. Select the labels that represent the user populations who will receive the Duo Mobile app.
-
Click Apply.
Create a Duo API Account
-
While still logged in to the Ivanti Endpoint Manager Mobile admin portal as an administrator, navigate to Devices & Users → Users.
-
Click the Add button and choose Add Local User on the pop-up menu.
-
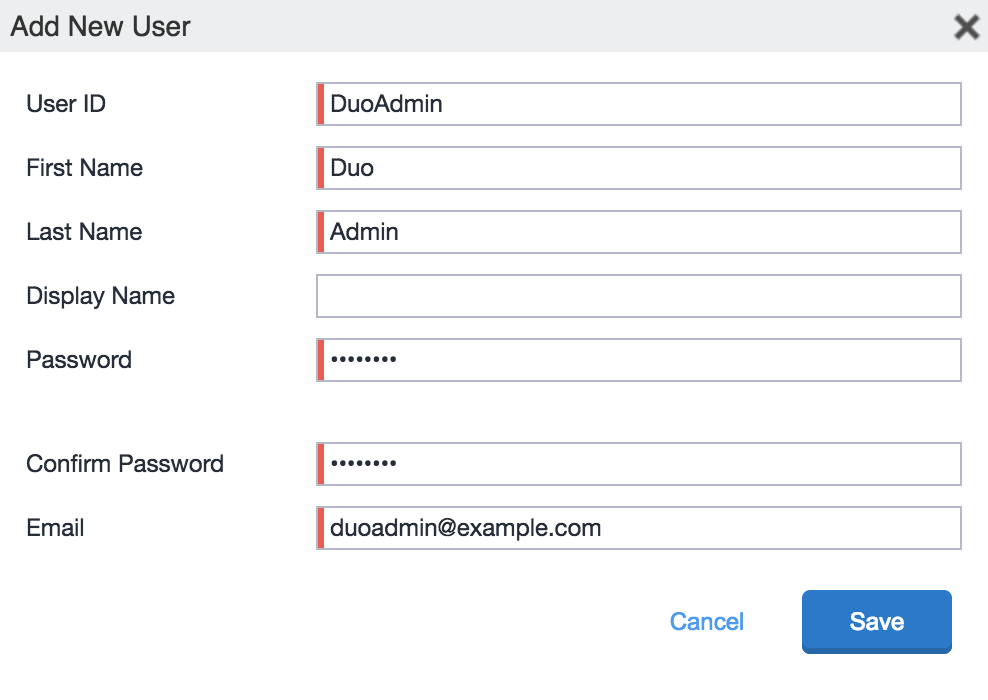
Enter the following information on the "Add New User" form:
User ID Enter the desired Duo account username. First Name and Last Name Enter a first and last name for the Duo API user (e.g. "Duo" "Admin"). Password and Confirm Password Enter and confirm a strong password for the Duo admin user. Email Address Enter an email address for the Duo admin user. -
Click the Done button to create the Duo admin user.
-
Navigate to Admin → Admins. Select the Duo Admin user you just created, click the Actions button, and then click Assign to Space.
-
Select a space from the "Select Space" drop-down list, and then check the box for the View device page, device details role under "Device Management". Click Save.
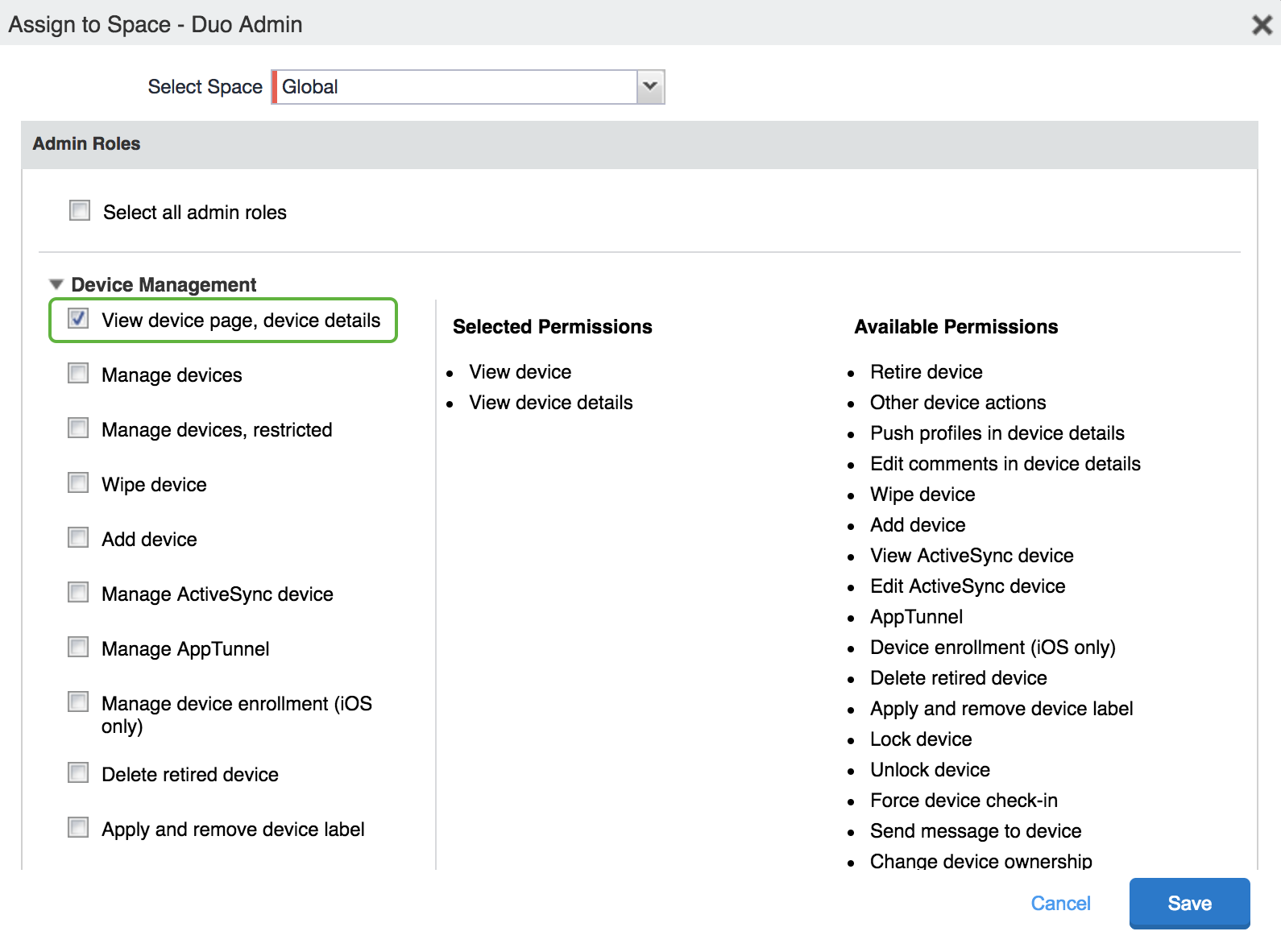
-
Repeat steps 5 and 6 for all available spaces that contain managed devices.
Enter Ivanti Endpoint Manager Mobile Info in Duo
-
Return to the Duo Admin Panel. Enter the following information into the blank fields in the "Enter API Details" section:
Local User Email Address Enter the email address (which is also the username) of the Duo admin user you created in Ivanti Endpoint Manager Mobile. Local User Email Password Enter the password for the Duo admin user you created in Ivanti Endpoint Manager Mobile. Ivanti Endpoint Manager Mobile Domain Name Enter your organization's Ivanti Endpoint Manager Mobile domain name. For example, acmecorp.mobileiron.com. -
Click the Test Configuration button to verify Duo's API access to your Ivanti Endpoint Manager Mobile instance. You'll receive a "Configuration Successful!" message if everything's correct. If the test fails, verify that you completed the Ivanti Endpoint Manager Mobile configuration steps and entered the right information in the Duo Admin Panel.
-
After you successfully test your configuration, click the Save & Configure button.
At this point the configured integration is disabled and applies to no users until you finish your deployment.
Verify iOS Device Information with Search
After you configure the connection between Ivanti Endpoint Manager Mobile and Duo you can verify that a given device's information is being pulled into Duo by searching for the device identifier from the Duo Admin Panel. See Search for Device Identifiers to learn how.
iOS Certificate Configuration
End of Life Information
New Ivanti Endpoint Manager Mobile (formerly known as MobileIron Core) certificate deployment management integrations may no longer be created as of October 2021. Consider migrating your certificate-based iOS Ivanti Endpoint Manager Mobile integration to Ivanti Endpoint Manager Mobile with App Config. See the Duo Knowledge Base article Guide to updating Trusted Endpoints iOS integrations from certificates to AppConfig for more information about migrating your iOS certificate-based management integrations to App Config.
These instructions remain available for customers who created these integrations before October 2021 and may need to reconfigure them. Duo continues to support existing Ivanti Endpoint Manager Mobile iOS certificate deployments and will do so until the integration reaches end-of-life status in a future update.
Duo verifies the trusted status of iOS devices by checking for the presence of a Duo device certificate. You'll use Ivanti Endpoint Manager Mobile to push the Duo CA information to your mobile devices so they can obtain a Duo certificate.
Create the Ivanti Endpoint Manager Mobile Integration
- Log in to the Duo Admin Panel and navigate to Trusted Endpoints.
- If this is your first management integration, click the Get started button at the bottom of the Trusted Endpoints introduction page. If you're adding another management integration, click the Add Integration button you see at the top of the page instead.
- On the "Add Management Tools Integration" page, locate Ivanti Endpoint Manager Mobile in the list of "Device Management Tools" and click the Add this integration selector.
- Choose Certs for iOS from the "Legacy" options, and then click the Add button.
The new Ivanti Endpoint Manager Mobile integration is created in the "Disabled" state. You'll turn it on when you're ready to apply your Duo trusted endpoints policy.
Keep the Duo Admin Panel open in your browser. You'll need to refer back to the Ivanti Endpoint Manager Mobile management integration page to complete the iOS configuration steps.
Add the Duo Certificate Authority
-
In the Ivanti Endpoint Manager Mobile admin portal, navigate to Policies & Configs → Configurations.
-
Go to Add New → Certificate Enrollment → SCEP.
-
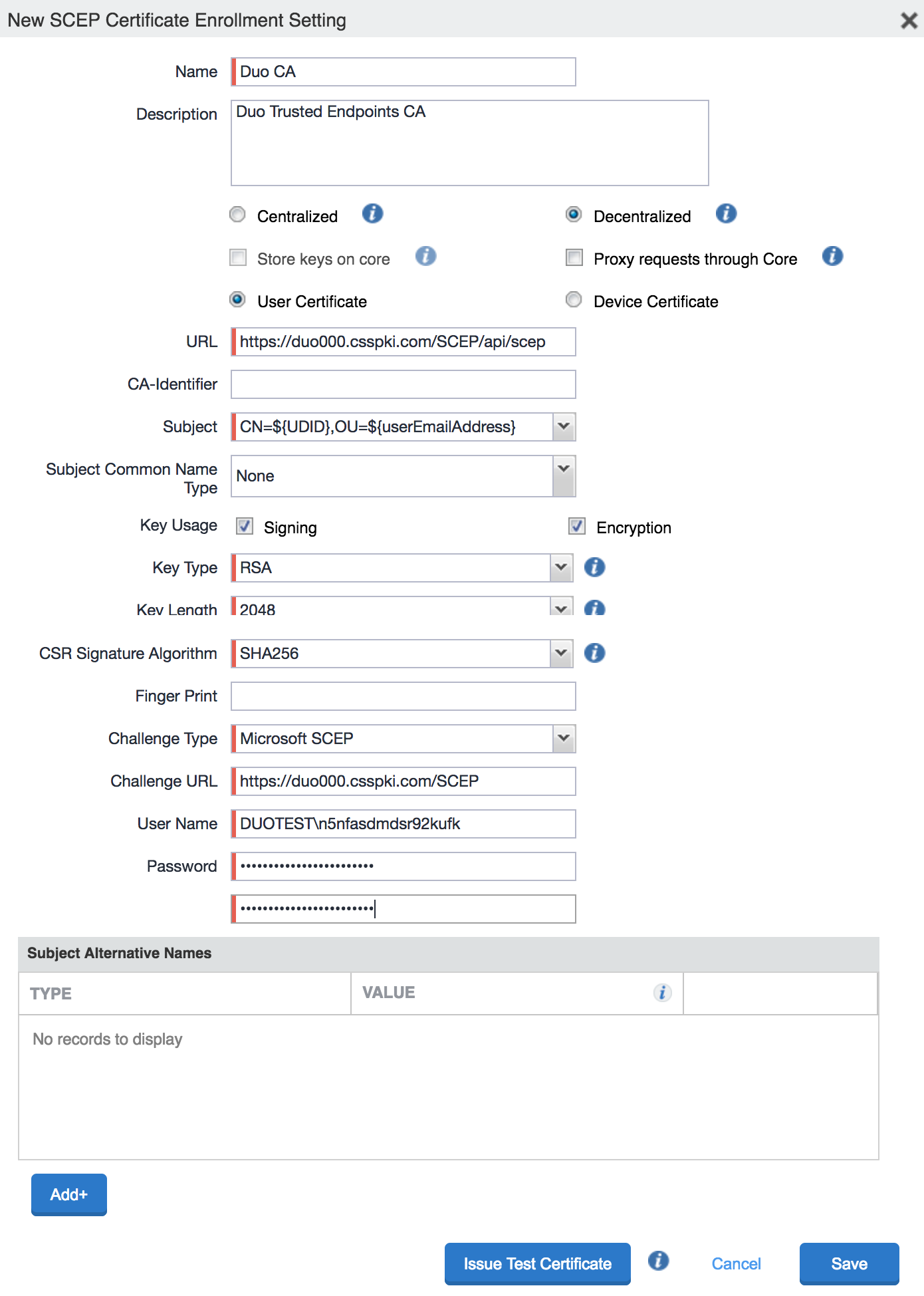
On the "Configurations" page, scroll down to the "New SCEP Certificate Enrollment Setting" section. Enter the Duo Certificate Authority (CA) information from step 2 of the "iOS Configuration Instructions" on the Ivanti Endpoint Manager Mobile management integration page in the Duo Admin Panel into the "New SCEP Certificate Enrollment Setting" form as follows:
Name Enter a descriptive name, like "Duo CA". Description Enter optional descriptive information about the Duo CA. Device Certificate Retrieval Decentralized Certificate Type User Certificate URL Paste in the SCEP URL from the "Add an External Certificate Authority (CA)" section of the iOS instructions on the Ivanti Endpoint Manager Mobile management integration page in the Duo Admin Panel. Subject Paste in the Subject from the "Add an External Certificate Authority (CA)" section of the iOS instructions on the Ivanti Endpoint Manager Mobile management integration page in the Duo Admin Panel. Key Type RSA Key Length 2048 CSR Signature Algorithm SHA256 Challenge Type Microsoft SCEP Challenge URL Paste in the Challenge URL from the "Add an External Certificate Authority (CA)" section of the iOS instructions on the Ivanti Endpoint Manager Mobile management integration page in the Duo Admin Panel. Username Paste in the Username from the "Add an External Certificate Authority (CA)" section of the iOS instructions on the Ivanti Endpoint Manager Mobile management integration page in the Duo Admin Panel. Password Paste in the Password from the "Add an External Certificate Authority (CA)" section of the iOS instructions on the Ivanti Endpoint Manager Mobile management integration page in the Duo Admin Panel. -
Click Issue Test Certificate after entering all the required information. If Ivanti Endpoint Manager Mobile is able to issue a Duo certificate successfully, click OK on the certificate page and then click Save to finish creating the Duo CA. If you receive a warning message about certificate caching, click Yes to proceed.
Apply the Duo CA Configuration
-
While still on the "Configurations" page, select the Duo CA you just created and click Actions → Apply to Label.
-
Select the device labels that include the iOS devices to which you want to issue Duo endpoint certificates.
-
Click Apply after selecting your iOS device groups for configuration distribution to queue the update.
At this point the configured integration is disabled and applies to no users until you finish your deployment.
Finish Trusted Endpoints Deployment
Once your Ivanti Endpoint Manager Mobile managed devices receive the Duo config you can set the Trusted Endpoints policy to start checking for managed device status as users authenticate to Duo-protected services and applications.
When your trusted endpoints policy is applied to your Duo applications, return to the Ivanti Endpoint Manager Mobile trusted endpoint management integration in the Duo Admin Panel. The "Change Integration Status" section of the page shows the current integration status (disabled by default after creation). You can choose to either activate this management integration only for members of a specified test group, or activate for all users. If you created more than one Ivanti Endpoint Manager Mobile integration, you must activate each one individually.
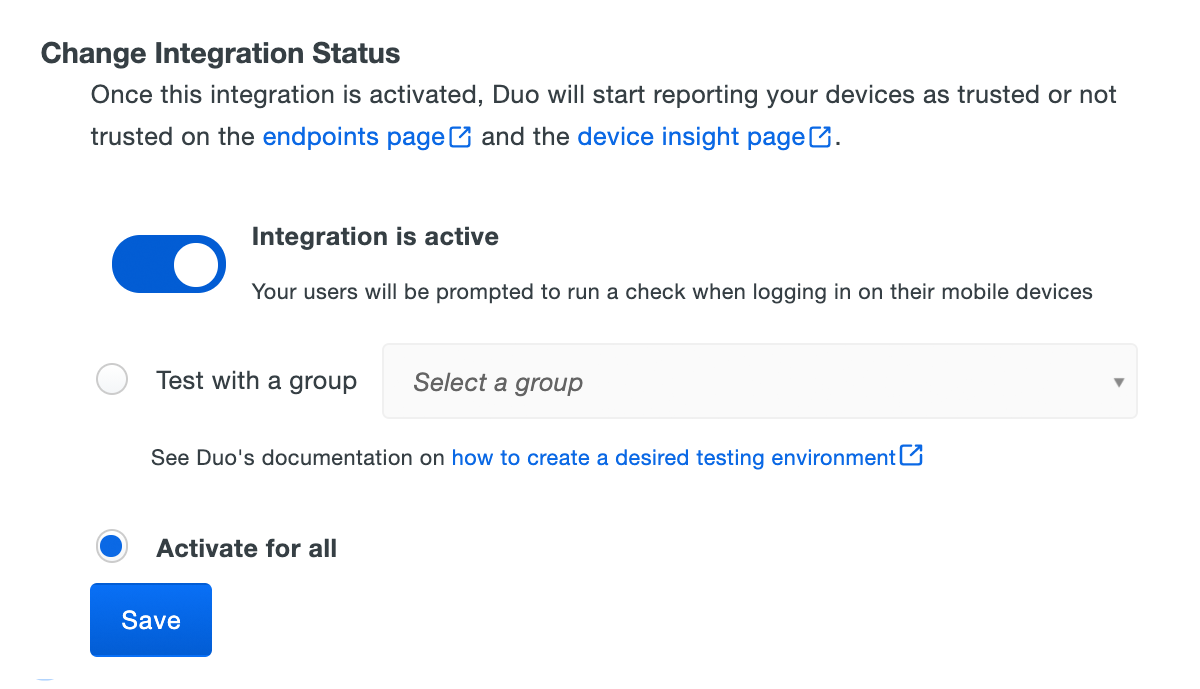
Duo Premier and Duo Advantage plans: The Device Insight and Endpoints pages in the Duo Admin Panel show which access devices are trusted/managed.
Verify Your Setup
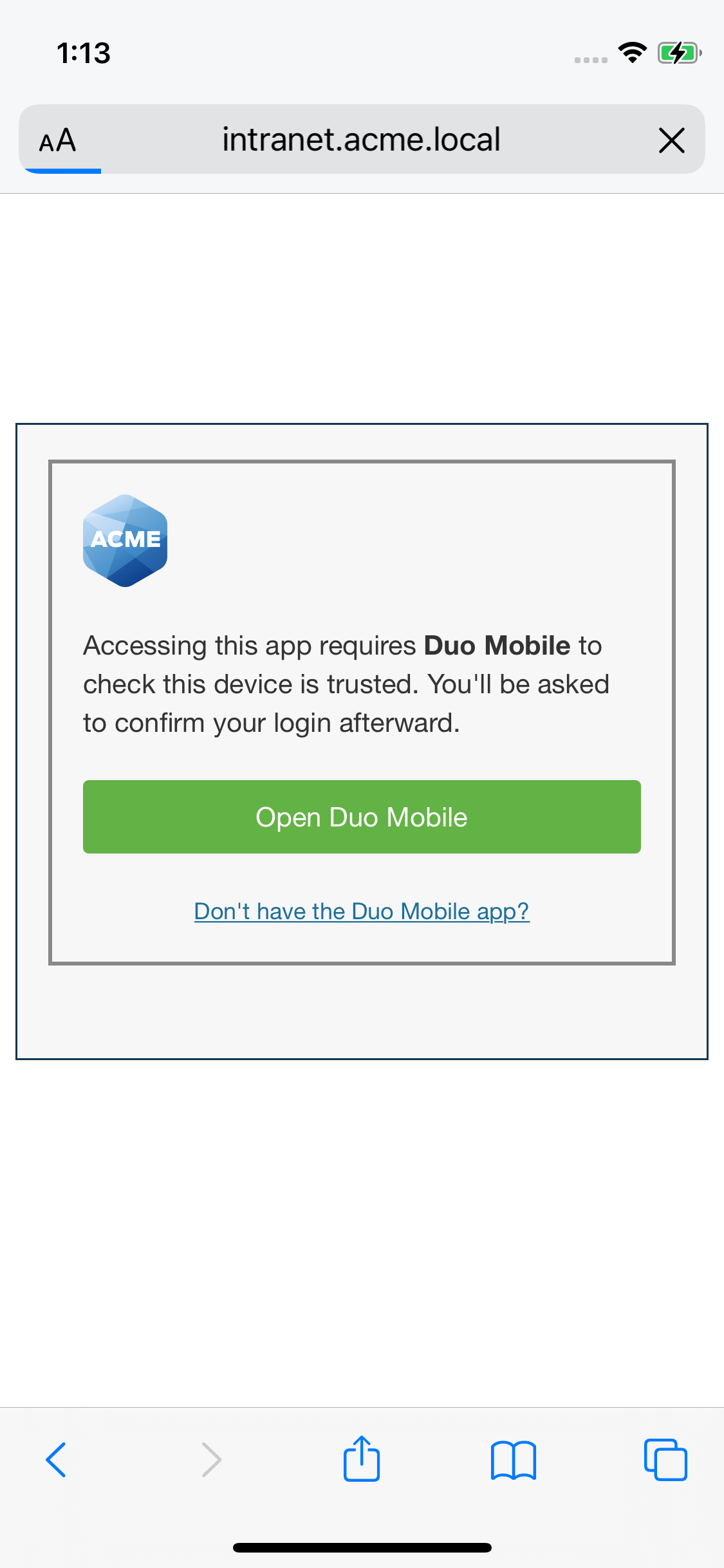
Users with Duo Mobile installed and activated for Duo Push on Android and iOS devices see a device trust dialog when authenticating to a protected resource via the Duo Prompt.
Duo uses the API access you granted in Ivanti Endpoint Manager Mobile to perform a permissions check to verify device information.
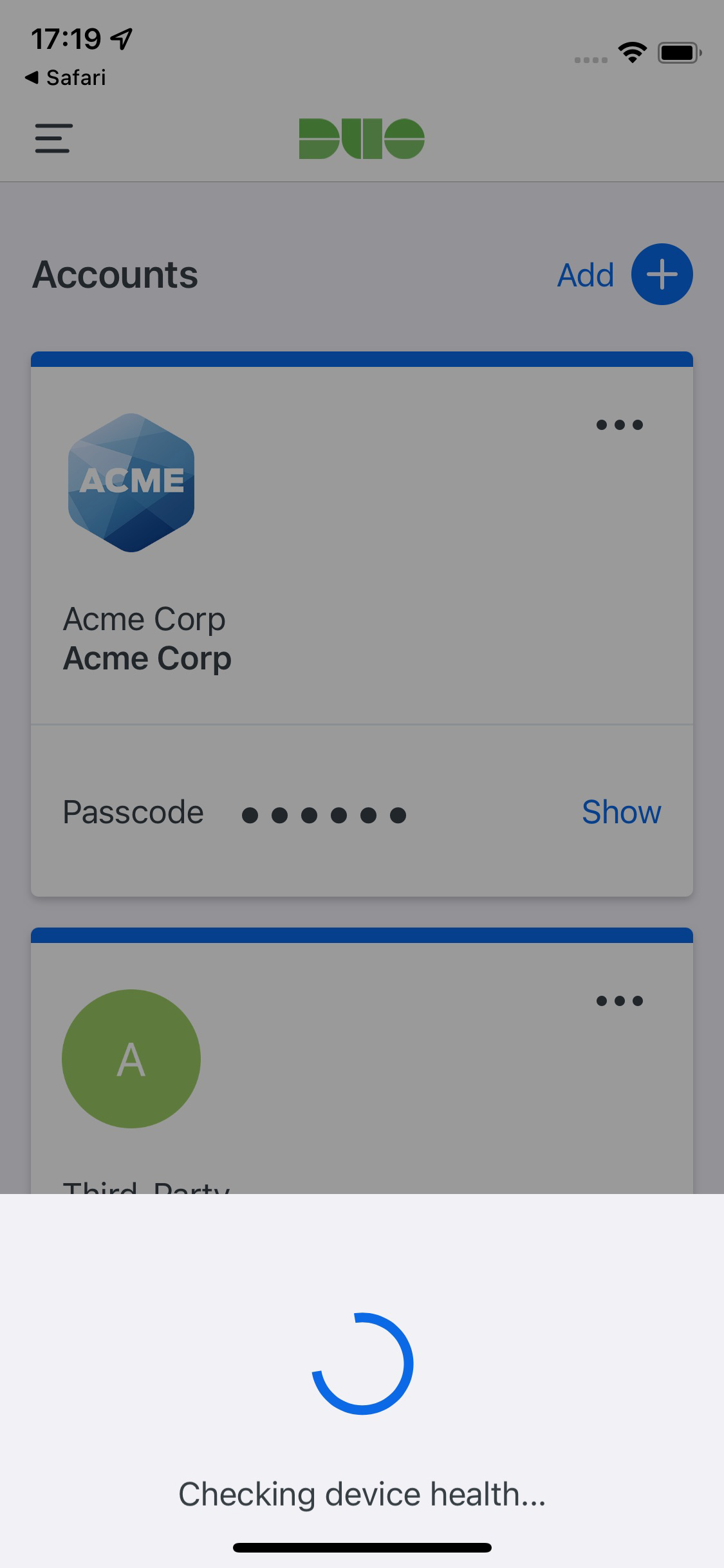
If Duo successfully verifies the device information using the Ivanti Endpoint Manager Mobile API access, and the user has Duo Mobile activated for Duo Push, then the user receives a login request on their phone.
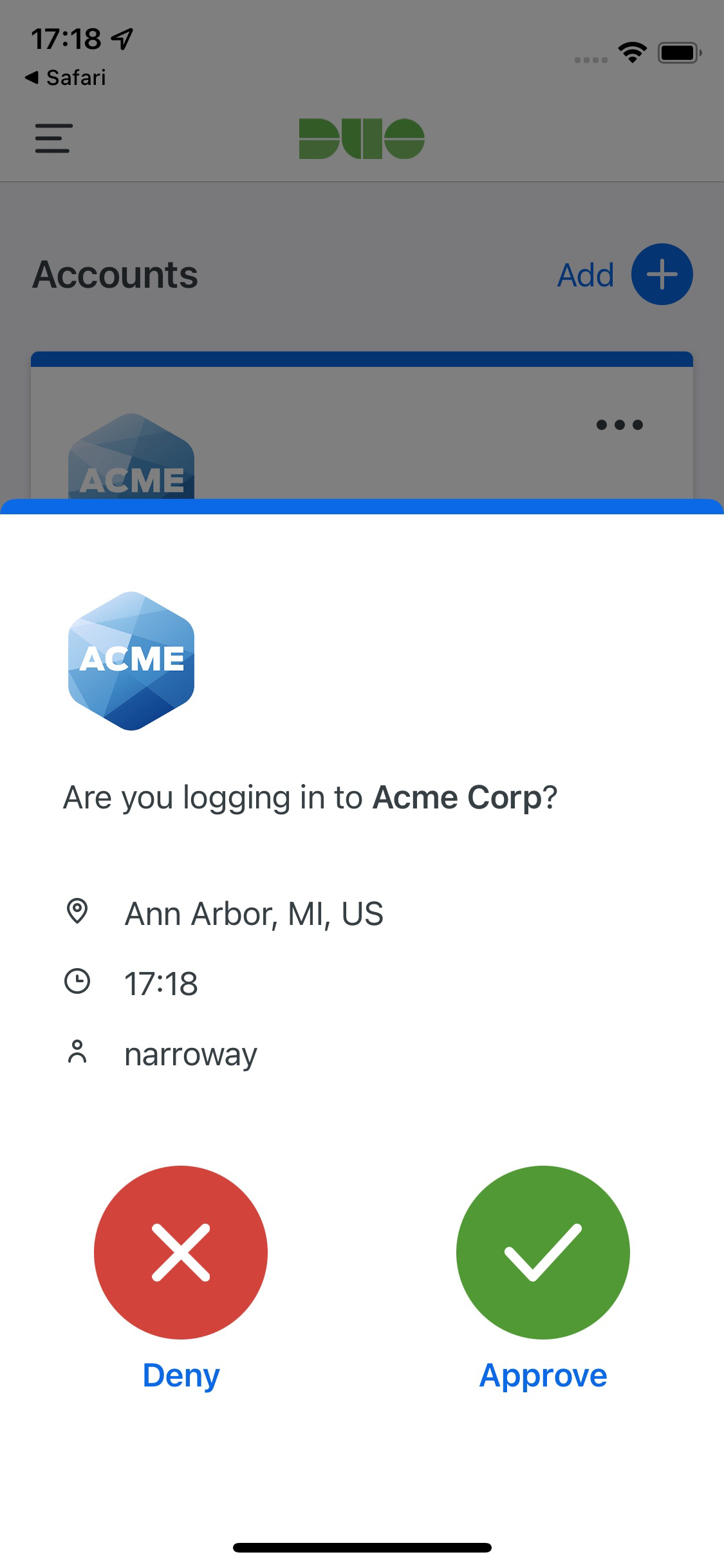
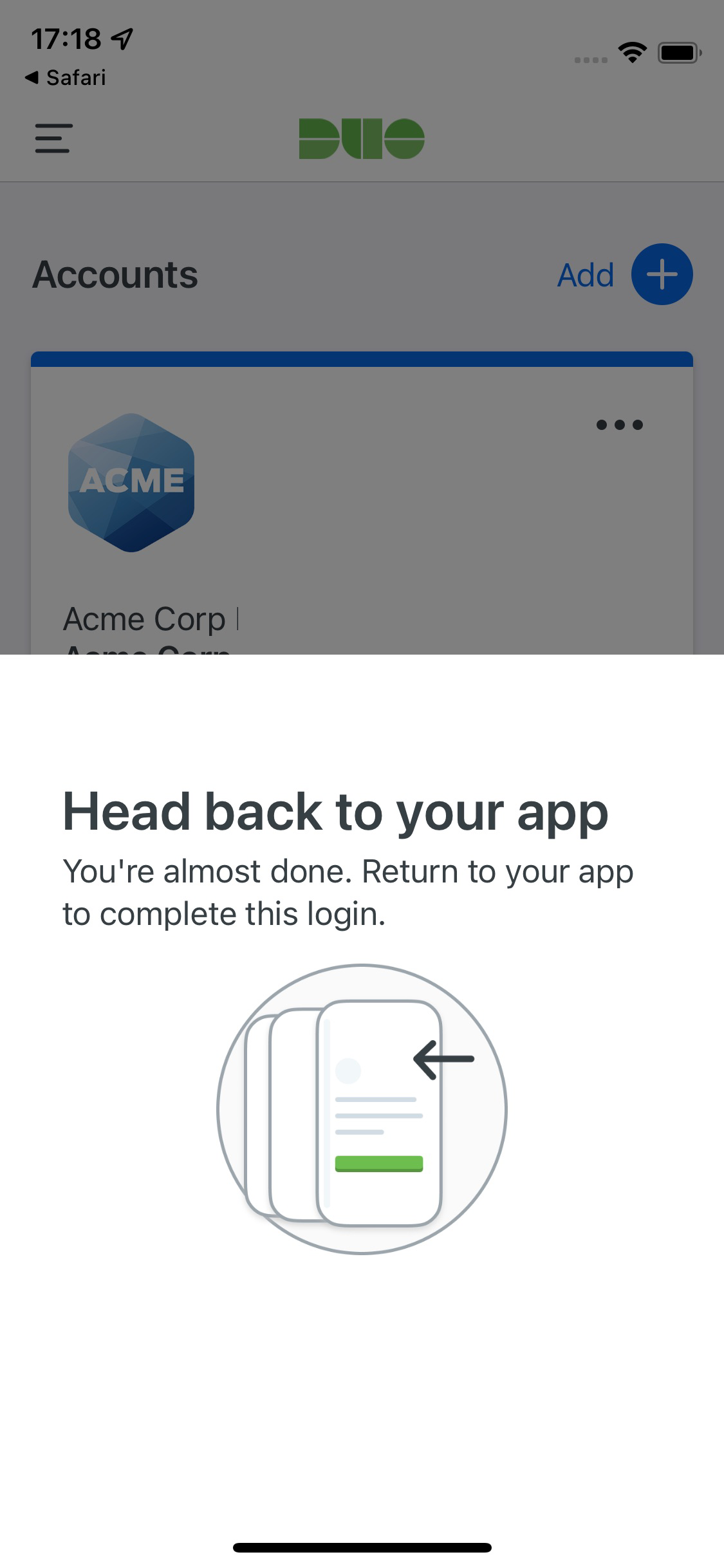
On Android devices, approving the request grants access and returns the user to the protected application. On iOS devices, after approving the Duo authentication request users tap the top-left of the Duo Mobile app to return to the application and complete login. The "Second Factor" logged for these approvals is shown as "Duo Mobile Inline Auth" in the Duo authentication log.
If the user does not have Duo Mobile activated for push, or does not approve the Duo request before it times out, the user returns to the Duo Prompt, where they may select from the available factors to complete 2FA.
With the legacy iOS certificate configuration, iOS users will see a prompt asking them to choose a certificate when authenticating to a protected resource via the Duo prompt. After selecting the Duo Device Authentication certificate and completing authentication, subsequent Duo authentications from the same device will automatically use that same certificate for verification.
Search for Device Identifiers
If you configured Duo Mobile for iOS with App Config or Android to determine device trust, you may want to search for specific device identifiers to verify that the identifier information for a given trusted device exists in Duo. This can be useful to verify a device you expect to be trusted was imported from Ivanti Endpoint Manager Mobile into Duo.
To search for a device identifier in Duo:
-
Log in to the Duo Admin Panel and navigate to Trusted Endpoints.
-
Locate the Ivanti Endpoint Manager Mobile or Ivanti Endpoint Manager Mobile with App Config device management integration you want to search for a device identifier in the list and click on it to view its details.
-
In the "Check if devices have synced" section, enter the identifier for the device you want to check and click Search.
-
A message appears indicating if the device identifier was either found or not found. If the device identifier is not found, check your Ivanti Endpoint Manager Mobile API configuration and wait 24 hours.
Use these instructions to find the device identifier to search in Ivanti Endpoint Manager Mobile.
- Log in to the Ivanti Endpoint Manager Mobile admin portal, navigate to Devices & Users, and expand a device to view.
- Under "Device Details", see "Device UUID".
- The "Device UUID" is the device identifier. Copy this value and use it to perform the search in Duo.
Removing the Ivanti Endpoint Manager Mobile Management Integration
Deleting a trusted endpoints management tool integration from the Duo Admin Panel immediately invalidates issued Duo device authentication certificates. Be sure to unassign your trusted endpoints policy from all applications or remove the "Trusted Endpoints" configuration item from your global policy before deleting an existing Ivanti Endpoint Manager Mobile integration from "Trusted Endpoints Configuration". You should also disable your Duo admin user in Ivanti Endpoint Manager Mobile.
Leaving the policy settings in place after deleting a management tools integration may inadvertently block user access to applications.
Troubleshooting
Need some help? Take a look at our Trusted Endpoints Knowledge Base articles or Community discussions. For further assistance, contact Support.
